Archive for October 2021
How Zero Trust Will Change Your Security Design Approach
How do you know what users, devices and apps to trust? As #cyberattacks get more advanced, businesses need to implement the right architectural model to stay protected. Here’s how. #ZeroTrust
Read MoreFull-Featured Managed Security Services with IBM
With so many #securitysolutions to choose from, how do you know which one will be right for you? Watch this video from IBM to see how they can meet your security needs while you grow your business. #IBMSecurity
Read MoreThe State of Data Security
Strategic data management drives #businessgrowth, but a #databreach can damage your brand, cripple ops, and reduce shareholder value. Learn what you can do to build a strong #datasecurity strategy. #IBMsecurity
Read MoreCost of a Data Breach
How much could a #databreach cost your business? Compiled from an analysis of over 537 real breaches, this definitive report is a must read to understand the breadth of a breach’s financial impact. #IBMsecurity
Read More5 Ways Cloud-Based IT Can Help Your Small Business
Companies that use cloud-based technology are 4x more productive. Download this @CiscoSMB infographic, brought to you by ETI, to learn 5 ways cloud-based IT can help your SMB.
Read MoreFive Common Data Security Pitfalls
What avoidable #datasecurity mistakes is your business making? Watch out for these 5 common pitfalls to stop #securitybreaches before they happen & contact an ETI #IBMsecurity expert to discuss solutions.
Read MoreBig Security in a Small Business World: 10 myth busters for SMB cybersecurity
Security report: 10 myth busters for SMB cybersecurity. Interested in learning more about how SMBs handle cybersecurity? Download this report, brought to you by ETI, for information from @CiscoSMB.
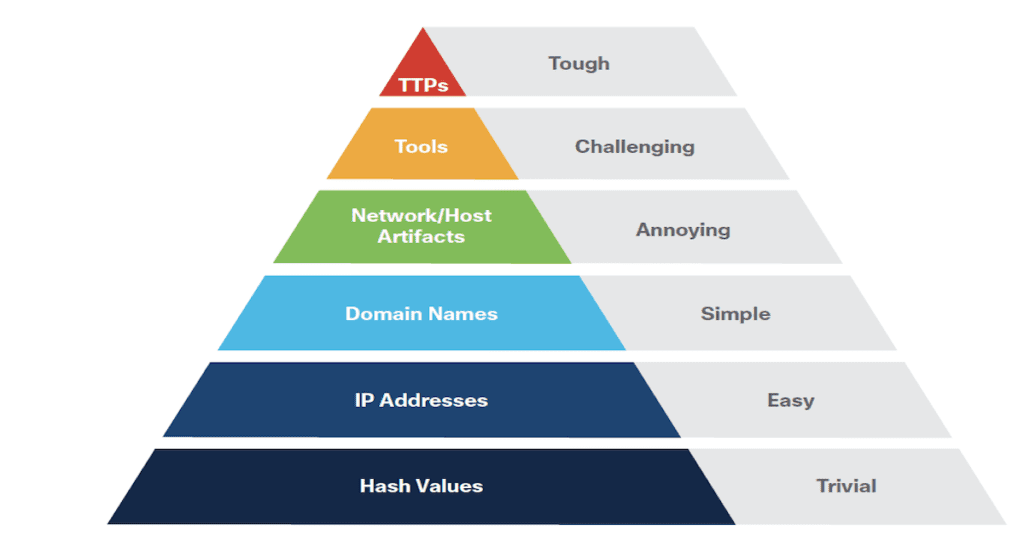
Read MoreStrategies for managing cybersecurity risk
Given the recent string of high-profile data breaches, #datasecurity is a hot topic. Yet many businesses still struggle to adopt a strategy that keeps their data secure. Read this eBook to facilitate your #security journey. #IBM
Read MoreHunting for Hidden Threats: Incorporating Threat Hunting Into Your Security Program
Eliminate threats before they’re a problem. This white paper, brought to you by ETI, discusses the threat-hunting discipline and describes how to build out effective threat-hunting campaigns. @CiscoSMB
Read MoreCase Study — Commercial International Bank S.A.E.
Is your business struggling to implement new #securitytech and leave outdated manual processes behind? Discover how one commercial international bank did it with the #IBMsecuritysolutions. #B2Bcasestudy
Read More